It was only a matter of time before ransomware attackers started targeting NAS devices, popular edge appliances used by enterprises and consumers alike for critical file and backup storage.
The NAS attacks began in June 2019 and focused mostly on QNAP devices, and then shifted gears toward Synology appliances in July, targeting a flaw in the company’s Linux-based management platform.
But no matter if you’re using QNAP, Synology, or any other NAS, there are a few ways to ensure your device isn’t the next one held for ransom.
Types of Ransomware
There are several types of ransomware that specifically target NAS devices. These include:
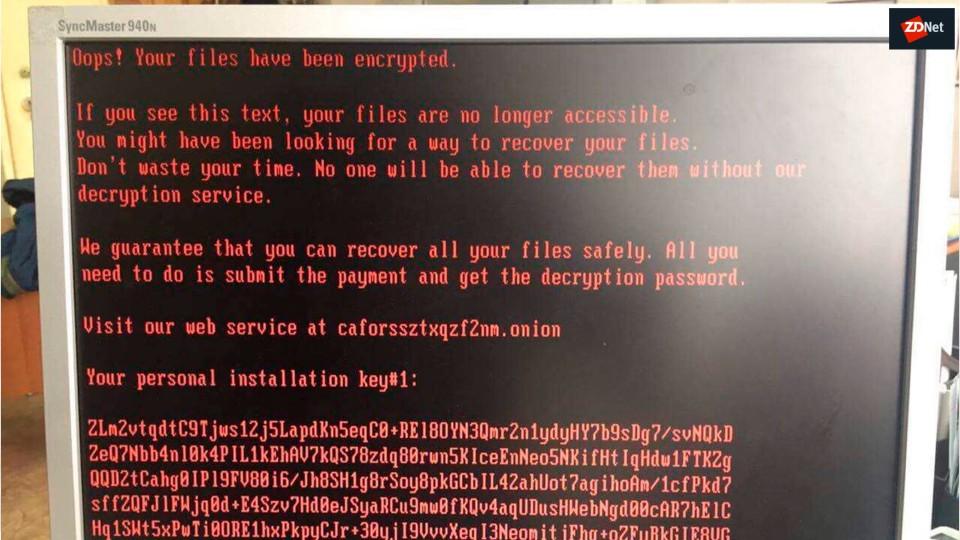
QNAPCrypt: As the name suggests, this ransomware specifically targets QNAP NAS devices. It encrypts files on the NAS and displays a ransom note demanding payment for the decryption key.
eCh0raix (QNAPCrypt v2): This ransomware is an evolution of the original QNAPCrypt, and also targets QNAP NAS devices. The name “eCh0raix” is related to the ransom note text used in this variant.
SynoLocker: SynoLocker was designed to target Synology NAS devices. Like the others, it encrypts files on the NAS and displays a ransom message, demanding payment in exchange for the decryption key.
Deadbolt: Deadbolt is another, more modern ransomware strain that is estimated to have infected thousands of QNAP NAS devices.
RTM: This group has recently developed ransomware to target Linux, NAS, and ESXi hosts.
What to Know About NAS and Ransomware
First, some background on NAS. Not all NAS devices are created with the same focus on security. Consumer-oriented NAS brands such as the recently attacked QNAP and Synology have the reputation of being less security minded than enterprise NAS vendors such as NetApp, Dell EMC and CTERA.
Enterprise NAS vendors obviously charge a premium, but this reflects the higher engineering costs that come from following strict and methodical development processes. Selling products to the enterprise and government markets involves going through strict security requirements, including specific regulations on the software development lifecycle and operating practices of the vendor, which allow you as a buyer to be more confident that your NAS vendor has security high on its list of priorities.
Steps to Protect Your NAS from Ransomware
So what can you do to prevent ransomware attacks on your NAS devices? Here are three steps for comprehensive NAS ransomware protection.
Download the CTERA Ransomware Solution Sheet
Disaster Recovery
With the threat of ransomware hovering continuously, for some organizations the question isn’t if ransomware will strike, but when. By having a disaster recovery solution in place, the major risks of ransomware are mitigated.
For example, CTERA’s disaster recovery solution ensures that its caching technology continuously replicates data to the cloud, offering near-immediate disaster recovery and ransomware mitigation following an attack – even when tens of terabytes need to be rolled back. As folders are rolled back, the edge filer is populated with stubs to give users immediate access to data without having to wait for full restoration.
The result is that when a user accesses an already-recovered portion of the data, it is immediately accessible; and for unrecovered portions, the data is recovered from the cloud in real-time, resulting in users not even noticing any downtime.
Immutable Snapshots
Immutable snapshots protect NAS devices and other backups from ransomware.
CTERA’s immutable snapshot capabilities mean that these snapshots are securely stored in immutable, air-gapped object storage; they are thus unable to be deleted or modified during the retention period, and are protected from any ransomware threat.
Zero Trust Architecture
Zero Trust Architecture (ZTA) is a security framework that assumes no implicit trust, even within a network perimeter, and requires strict verification and continuous monitoring of all users, devices, and applications attempting to access resources.
CTERA provides this – indeed, it is the only global filesystem to offer Zero Trust architecture – as edge filers never store or receive credentials for the object storage, and all storage operations are performed with single-use tokens provided by an authorization service in the CTERA Portal.
Protecting Cloud Data
Ransomware can encrypt files and data on a wide range of targets, from on-premises NAS devices to cloud-based storage.
What’s more, if a NAS device is connected to a network that has access to cloud-based storage services, and the NAS itself becomes infected with ransomware, it can potentially spread the ransomware to the connected cloud storage.
Once again, this demonstrates the need for holistic cybersecurity measures, proactive defense strategies, and choosing the right partners and vendors to ensure the highest levels of protection.
Download the CTERA NAS Know-It-All Kit.
As the leading provider of cloud-enabled NAS devices, CTERA is very familiar with building secure and compliant edge filer appliances for enterprises. Based on our experiences working with the world’s most security-conscious organizations, here are some questions you should ask your NAS vendor as you evaluate your current security model:
- Are you performing periodical security assessment by a 3rd party penetration testing lab? And if so, can I see your latest report?
- Do you have FIPS certification?
- Do you have reference customers in the U.S. federal and defense branches, or other government agencies?
- Do you have reference customers in financial sector, such as banks and insurance companies?
- Do you offer an SLA for time from a vulnerability is discovered until a security patch is provided?
If your vendor answers “Yes” to all of these questions, you can be much more confident that security was indeed a design goal rather than an afterthought in the engineering of this product.
Additional Tips on How to Protect NAS from Ransomware
- Ensure your NAS device is regularly updated with the latest firmware. If your NAS vendor offers an automatic updates service, use it.
- Ensure your users choose strong passwords, and require them to rotate their passwords regularly. We recommend using Active Directory, and to avoid using local users on the NAS device as much as possible. In Active Directory it is easy to enforce password complexity and require password rotations.
- Ensure your NAS device is configured to automatically block users trying to guess password using “brute force” – the means of attack on Synology devices – after several attempts.
Get Started with NAS Ransomware Protection
Ransomware protection is a vital component of IT operations. And with NAS devices often serving as repositories for critical data, an attack on a NAS can lead to the loss of valuable files, sensitive information, and potentially disrupt essential operations – not to mention leading to the infection of all cloud data.
To recap, we explored:
- The types of ransomware targeting NAS
- What you need to know about NAS ransomware
- How to protect NAS from ransomware
- Protecting cloud data
- Additional tips
Keep your NAS systems up-to-date and hold your vendors accountable. If you’d like to learn more about CTERA’s military-grade security and how you can leverage this for your organization, get in touch with a product expert today.
Glossary
NAS Ransomware: NAS Ransomware refers to a type of malicious software designed to target Network-Attached Storage (NAS) devices. It encrypts or locks files stored on these devices, rendering them inaccessible until a ransom is paid to obtain a decryption key.
Immutable Snapshots: Immutable snapshots are read-only copies of data taken at a specific point in time, typically on storage systems or platforms like NAS devices. These snapshots cannot be altered, deleted, or encrypted, even by malicious software like ransomware. Immutable snapshots serve as an effective data protection mechanism, ensuring that a clean and secure version of the data is always available for recovery.
Zero Trust Architecture (ZTA): Zero Trust Architecture is a cybersecurity framework and mindset that assumes no inherent trust, even within a network perimeter. It requires continuous verification and strict access controls for users, devices, and applications attempting to access resources. ZTA challenges the traditional network security model by focusing on identity verification, least privilege access, micro-segmentation, and continuous monitoring.
Related Resources
- Protect Your Data Against Ransomware with a Secure Edge-to-Cloud Strategy
- Costly Ransomware Attacks Expose Basic Misconceptions about Data Protection
- Leading U.S. construction firm recovers from ransomware using earthbend backup services powered by CTERA