Cyber-Resilient Storage
Founded by cybersecurity experts, CTERA fundamentally understands the value of data privacy, security, compliance and access controls. We enable not only enterprises to harness the benefits of cloud-based file management without the security compromises associated with traditional cloud offerings, but provide military grade encryption enabling defense forces worldwide to enjoy the benefits of CTERA.

A Security-First Approach To Protect Your Critical Data
Private Cloud
CTERA delivers an entirely private solution - deployed 100% within your firewall - on any on-premises or cloud infrastructure. No third party has access to your data, metadata, encryption keys, or authentication - ever.
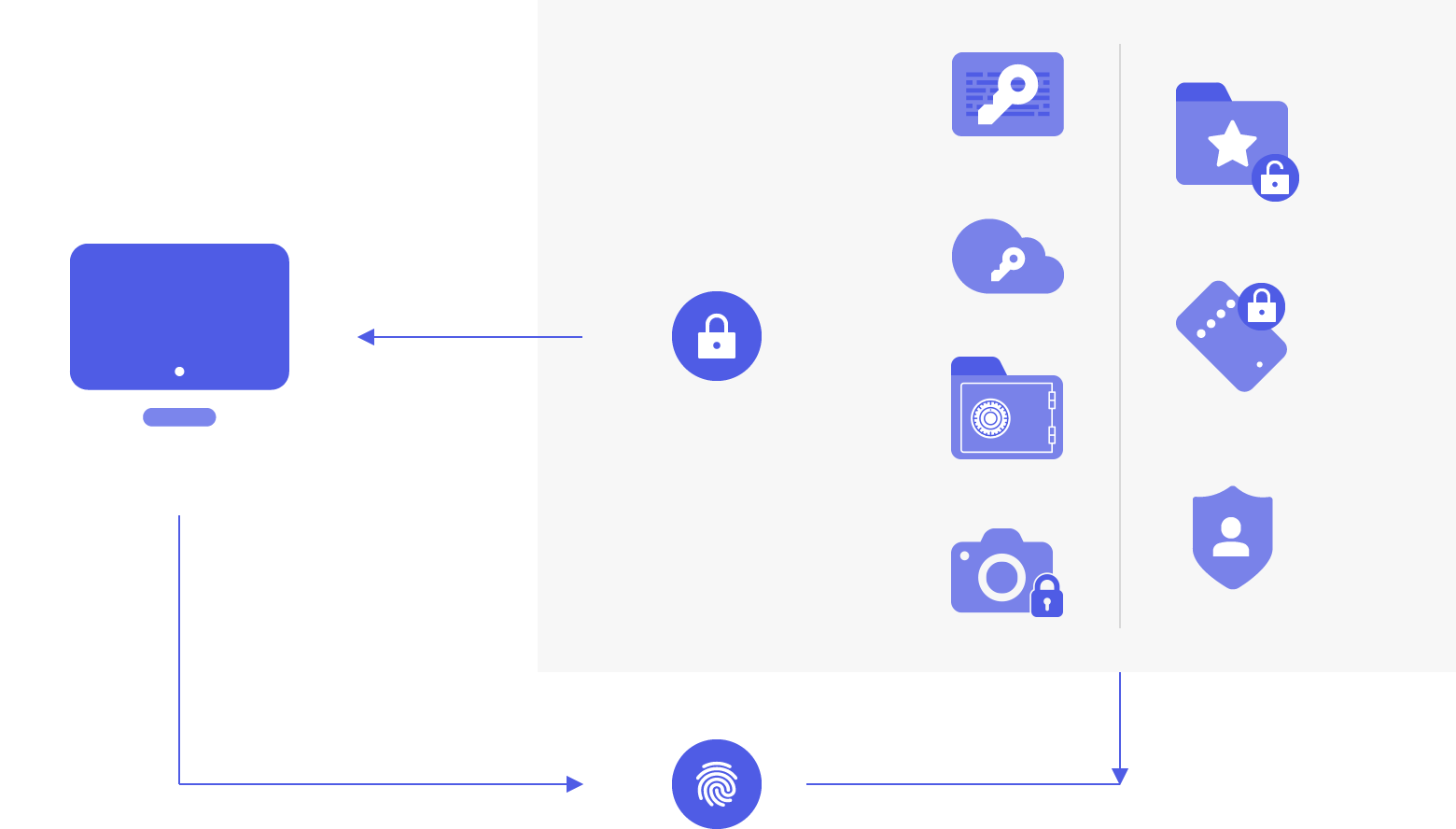
Military-Grade Encryption
Source-based encryption at rest (AES-256) and in transit (TLS 1.2) secures your data before it leaves your devices, offices and servers. CTERA’s private key management keeps data away from prying eyes.
Data Governance
Facilitate compliance and data governance with role-based access control and granular event logging to govern storage and collaboration.
All the Compliance You Need

Feature Highlights
Your Choice of Cloud
Deploy on-premises or in a virtual private cloud (VPC) to keep your data within your network and 100% behind your firewall.
Single Sign-On (SSO)
Use your favorite SSO and ID management tools to provide seamless user authentication and avoid duplicate credentials.
Source-based AES-256 encryption
Ensure that data is encrypted before it is sent to the cloud and while it is stored.
In-Transit TLS Encryption
Secure all WAN transfers using Transport Layer Security (TLS) protocol to prevent unauthorized interception of data transfers.
Zero Trust Architecture
'Never Trust, Always Verify:' edge devices are not given default privileges. Every access request requires digital signatures to perform the requested activity directly with the object storage.
Private Encryption Key Management
Manage your own encryption keys or use personal passphrases per user to prevent privileged admins from accessing data.
Two-Factor Authentication for File Sharing
Use email and SMS-based two-factor authentication for external file sharing to ensure only intended parties can access files.
SHA-1 Data Fingerprinting
Ensures data integrity as it travels between locations, prevents man-in-the-middle attacks and transfer errors.
Role-Based Access Control
Use Active Directory or LDAP roles and groups to control access to data and set up administrator roles.
Password Policy Enforcement
Set minimum password length and complexity, and enforce password change frequency.
Granular Event Logging
Monitor and log security events such as user access and failed logins, and integrate with SIEM systems via Syslog for 3rd party audit trail retention and reporting.
3rd Party Security Integrations
Integrate with leading Anti-Virus and EMM tools to ensure data security and governance.
CTERA Vault
WORM (Write Once Read Many) protection that allows data to be written to a storage system once, preventing modifications and/or deletions.
Immutable Snapshots
Securely store snapshots in immutable, air-gapped object storage, that cannot be deleted or modified during the retention period.
Related Resources