CTERA Recognized as Strong Performer on Gartner® Peer Insights™
Read Press ReleaseCTERA Erases the Boundary Between File and Object
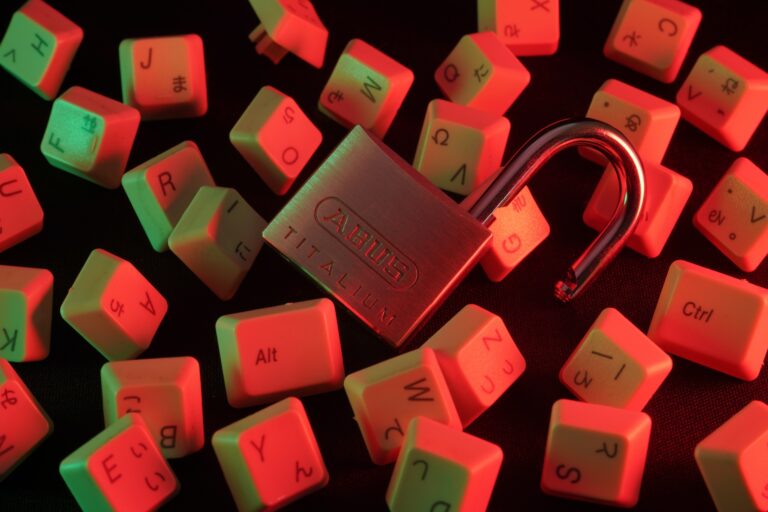
Read Press ReleaseTag: ransomware Library
TAGS
Authors

Aron Brand
(55)

Mike Ivanov
(22)

Oded Nagel
(14)

Kyle Edsall
(10)

Ravit Sadeh
(8)
CTERA Networks
(9)

Julian Weiss
(5)

Saimon Michelson
(5)

Alex Berman
(5)
Guest Author
(3)

Shlomi Ako
(2)

Justin Flynn
(2)

Shira Hayon
(2)
James Sadov
(2)

Cheryle Cushion
(2)

Mickael Benchetrit
(1)

Michael Amselem
(1)

Joe Scott
(1)

Robin Stone
(1)

Shai Zur
(1)

Gal Yosef
(1)

Tal Moshe
(1)

Dana Racine
(1)

Amir Goldstein
(1)