Defining SAML Single Sign-on in a CTERA Portal
To configure SAML single sign-on:
1 Select Settings > SSO from the menu.
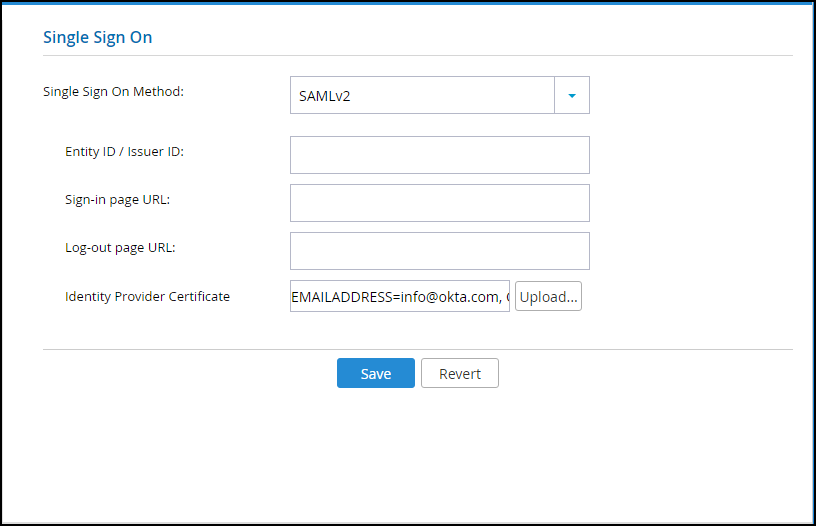
2 Select SAMLv2 from the dropdown box.
3 Enter the details of the SAML identity provider:
Entity ID/Issuer ID – The identity provider that issues the SAML assertion. This is a free text string that uniquely identifies your SAML identity provider and must match the entity ID that you choose when signing up for the identity provider's SSO service.
Okta – The Service Provider Entity Id value.
OneLogin – The SAML Audience value.
ADFS – The Relying party trust identifier value. For example, https://exampleportal.ctera.me/adfs/ls/IdpInitiatedSignOn.aspx
Sign-in page URL – The URL that CTERA Portal redirects to when signing in. You need to get this from the provider.
Okta –The EMBED LINK value.
OneLogin – The SAML 2.0 Endpoint (HTTP) value.
ADFS – The Endpoint value. For example, https://exampleportal.ctera.me/ServicesPortal/saml.
Log-out page URL – The URL that CTERA Portal redirects to when logging out of the portal. Without this URL configured, a logout will redirect to the sign-in page URL and log the user back into the portal.
Okta – Either the default Okta sign-out page is used or a customized sign-out page defined in Okta.
OneLogin – The SAML Single Logout URL value. This is optional.
ADFS – The logout URL. This is the same as the Sign-in Page URL.
Identity Provider Certificate – The authentication certificate issued by the provider. You need to get this from the provider, usually by download from the provider's site. .pem and .cer certificates are valid. Click Upload to upload your provider's certificate to the portal.
Okta – The certificate downloaded from Okta and converted to .pem.
OneLogin – The X.509 PEM certificate downloaded from OneLogin.
ADFS – The Token-signin certificate from the ADFS .cer certificates saved to a file. This certificate must be a known root CA and not a self-signed certificate.
4 Click Save.
Note: When the SAML identity provider is also connected to Active Directory, the user name to log in to the portal must be defined in the portal.